 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
IMAP General Operation, Client/Server Communication and Session States
(Page 2 of 3)
Session States
The session between an IMAP4 client and server is described in the IMAP standards using a finite state machine (FSM), a descriptive tool that I explain in the TCP operational overview. Again, this is similar to how the operation of POP3 is explained, except that IMAP4 is a bit more complex. Its FSM defines four states instead of three, and where a POP3 session is linear (only going through each state once) in IMAP4 the session is not. However, the state flow is still fairly straight-forward, mostly following a logical sequence from one state to the next. The IMAP FSM is illustrated in Figure 309.
|
The following are the IMAP states, in the usual sequence in which they occur for a session:
- Not Authenticated State:
The session normally begins in this state after a TCP connection is
established, unless the special IMAP preauthentication feature
has been used (we’ll get to this feature shortly). The client at
this point cannot really do much aside from providing authentication
information so it can move to the next state.
- Authenticated State:
The client has completed authentication, either through an authentication
process in the prior state or through preauthentication. The client
is now allowed to perform operations on whole mailboxes. The client
must select a mailbox before individual message operations are permitted.
- Selected State: After
a mailbox has been chosen, the client is allowed to access and manipulate
individual messages within the mailbox. When the client is done with
the current mailbox it can close it and return to the Authenticated
state to select a new one to work with, or can log out to end the session.
- Logout State: The client may issue a Logout command from any of the other states to request that the IMAP session be ended. The session may also enter this state if the session inactivity timer expires. The server sends a response and the connection is terminated.
Of the four IMAP states, only the first three are “interactive”, meaning states where commands are actively issued by the client and responses provided by the server. Some IMAP commands can be used while the session is in any state, while others are state-specific. The next topic describes IMAP commands and responses in general terms.
|
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.







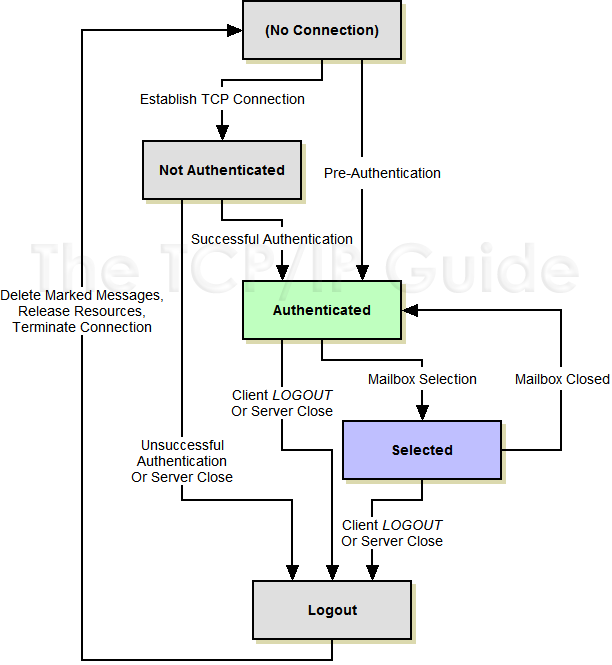
 Key Concept: IMAP is a client/server application, and an IMAP session begins with the client making a TCP connection to the server. The session then normally starts in the Not Authenticated state and remains there until successful authentication. In the Authenticated state, the client may perform operations on whole mailboxes, but a mailbox must be selected to transition to the Selected state where individual messages can be manipulated. The client can work with many mailboxes by selecting each one in turn; it then logs out from the server.
Key Concept: IMAP is a client/server application, and an IMAP session begins with the client making a TCP connection to the server. The session then normally starts in the Not Authenticated state and remains there until successful authentication. In the Authenticated state, the client may perform operations on whole mailboxes, but a mailbox must be selected to transition to the Selected state where individual messages can be manipulated. The client can work with many mailboxes by selecting each one in turn; it then logs out from the server.