 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
POP3 Authorization State: User Authentication Process and Commands
(Page 2 of 3)
Standard POP3 Authentication
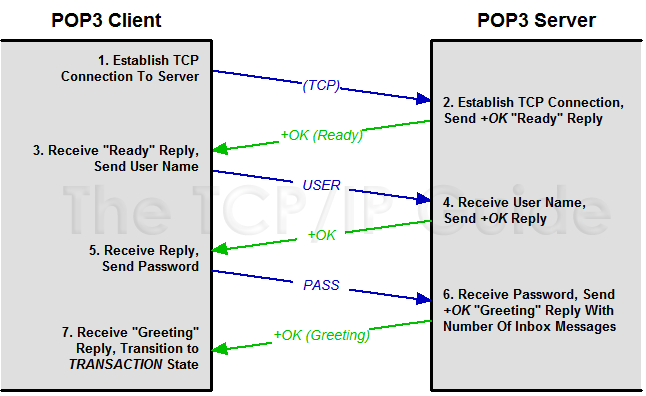
The normal method of authorization in POP3 is a standard “username / password” login. This is pretty much identical to how a login is performed in FTP; even the commands are the same. First the client issues a USER command along with the user's mailbox name (his or her user name or e-mail address). The server responds with an intermediate acknowledgment. The client then uses the PASS command to send the user's password. Assuming the login is valid, the server responds to the client with an acknowledgment that indicates successful authentication. The response will also typically specify the number of messages waiting for the user in the mailbox. This process is illustrated in Figure 307.
|
Table 256 shows an example POP3 authorization, with the client's commands highlighted and the server's responses in italics.
+OK POP3
server ready |
|
If authorization is successful, the POP3 session transitions to the Transaction state where mail access commands can be performed. If the user name or password are incorrect, an error response is given and the session cannot proceed. The authorization may also fail due to technical problems, such as an inability by the server to lock the mailbox (perhaps due to new mail arriving via SMTP).
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.







 Note: Some servers may require only the name of the user (“jane”) while others require the full e-mail address as shown in the example. Also, I have not shown Jane's password in
Note: Some servers may require only the name of the user (“jane”) while others require the full e-mail address as shown in the example. Also, I have not shown Jane's password in