 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
FTP Control Connection Establishment, User Authentication and Anonymous FTP Access
(Page 2 of 3)
FTP Login Sequence and Authentication
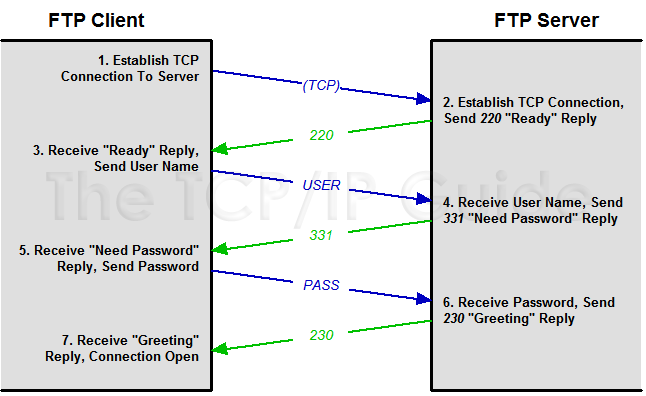
FTP’s regular authentication scheme is quite rudimentary: it is a simple “username / password” login scheme, shown in Figure 289. Most of us are familiar with this type of authentication for various types of access, on the Internet and elsewhere. First, the user is identified by sending a user name from the User-PI to the Server-PI using the USER command. Then, the user's password is sent using the PASS command.
|
The server checks the user name and password against its user database, to verify that the connecting user has valid authority to access the server. If the information is valid, the server sends back a greeting to the client to indicate that the session is opened. If the user improperly authenticates (by specifying an incorrect user name or password), the server will request that the user attempt authorization again. After a number of invalid authorization tries, the server may time out and terminate the connection.
Assuming that the authentication succeeds, the server then sets up the connection to allow the type of access to which the user is authorized. Some users may have access to only certain files or certain types of files. Some servers may allow particular users to read and write files on the server, while other users may only retrieve files. The administrator can thus tailor FTP access as needed.
Once the connection is established, the server can also make resource selection decisions based on the user's identity. For example, on a system with multiple users, the administrator can set up FTP so that when any user connects, he or she automatically is taken to his or her own “home directory”. The optional ACCT (account) command also allows a user to select a particular account if he or she has more than one.
Like most older protocols, the simple login scheme used by FTP is a legacy of the relatively “closed” nature of the early Internet. It is not considered secure by today's global Internet standards, because the user name and password are sent across the control connection in clear text. This makes it relatively easy for login information to be intercepted by intermediate systems and accounts to be compromised. RFC 2228, FTP Security Extensions, defines more sophisticated authentication and encryption options for those who need added security in their FTP software.
|
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.







 Key Concept: An FTP session begins with the establishment of a control connection between an FTP client and server. After the TCP connection be made, the user must authenticate with the server, using a simple user/password exchange between client and server. This provides only rudimentary security, so if more is required, it must be implemented using FTP security extensions or through other means.
Key Concept: An FTP session begins with the establishment of a control connection between an FTP client and server. After the TCP connection be made, the user must authenticate with the server, using a simple user/password exchange between client and server. This provides only rudimentary security, so if more is required, it must be implemented using FTP security extensions or through other means.