|
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
IPSec Encapsulating Security Payload (ESP)
(Page 4 of 4)
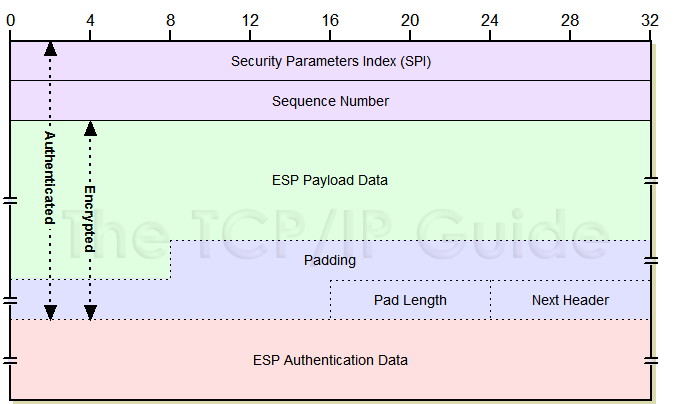
Encapsulating Security Payload Format
The format of the ESP sections and fields is described in Table 80 and shown in Figure 126. I have shown explicitly in each the encryption and authentication coverage of the fields, which will hopefully cause all that stuff I just wrote to make at least a bit more sense.
Section |
Field Name |
Size (bytes) |
Description |
Encryption Coverage |
Authentication Coverage |
ESP Header |
SPI |
4 |
Security Parameter Index (SPI): A 32-bit value that is combined with the destination address and security protocol type to identify the security association to be used for this datagram. See the topic on security associations for more details. |
|

|
Sequence Number |
4 |
Sequence Number: A counter field initialized to zero when a security association is formed between two devices, and then incremented for each datagram sent using that SA. This is used to provide protection against replay attacks. |
|
||
Payload |
Payload Data |
Variable |
Payload Data: The encrypted payload data, consisting of a higher layer message or encapsulated IP datagram. May also include support information such as an initialization vector, required by certain encryption methods. |

|
|
ESP Trailer |
Padding |
Variable (0 to 255) |
Padding: Additional padding bytes included as needed for encryption or for alignment. |
||
Pad Length |
1 |
Pad Length: The number of bytes in the preceding Padding field. |
|||
Next Header |
1 |
Next Header: Contains the protocol number of the next header in the datagram. Used to chain together headers. |
|||
ESP |
Variable |
ESP Authentication Data: This field contains the Integrity Check Value (ICV) resulting from the application of the optional ESP authentication algorithm. |
|
|
|
|
The Padding field is used when encryption algorithms require it. Padding is also used to make sure that the ESP Trailer ends on a 32-bit boundary. That is, the size of the ESP Header plus Payload plus ESP Trailer must be a multiple of 32 bits. The ESP Authentication Data must also be a multiple of 32 bits.
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.